Audit Events
Audit Events
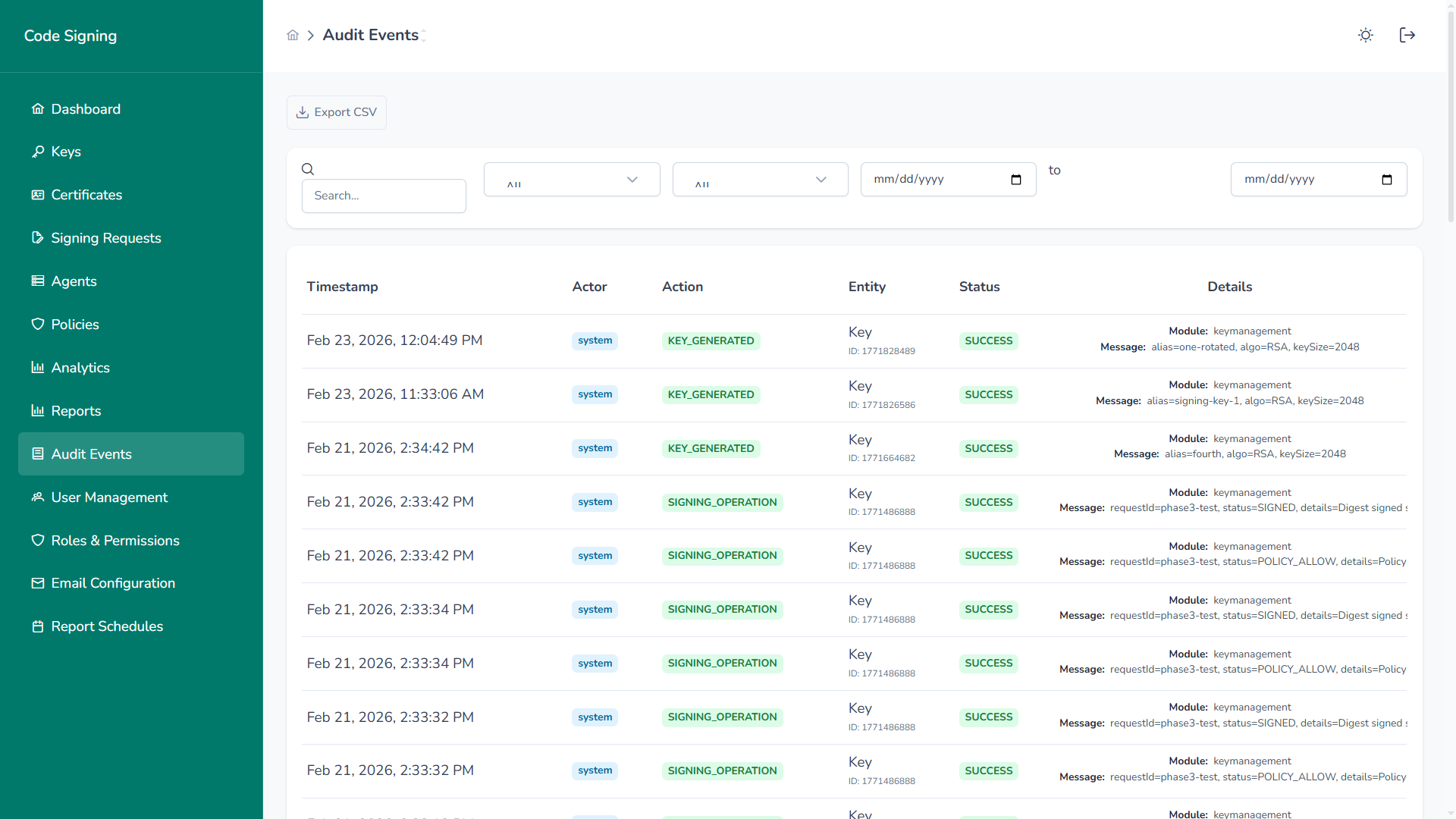
Section titled “Audit Events”The Audit Events interface provides a complete, tamper-resistant record of all platform activity across signing operations, keys, certificates, users, and policies.
Overview
Section titled “Overview”Every security-relevant and operational action is recorded, including:
- Signing operations
- Key lifecycle events
- Certificate management
- Policy enforcement
- User activity
- Agent events
- System changes
This ensures full traceability across the entire code signing lifecycle.
Event Structure
Section titled “Event Structure”Each audit record includes:
- Timestamp – Precise event time
- Actor – User, service account, or system
- Action – Operation performed (e.g.,
KEY_GENERATED,SIGNING_OPERATION) - Entity – Affected object (Key, Certificate, Policy, Agent)
- Status – Success, Failure, Denied
- Details – Contextual metadata (module, algorithm, key size, request ID, policy result)
This structured format allows fast investigation and compliance validation.
Signing Audit Trail
Section titled “Signing Audit Trail”Every signing request logs:
- Request ID
- Digest algorithm
- Key ID used
- Policy evaluation result
- Approval workflow result (if applicable)
- Agent involved
- Final signing status
This enables complete end-to-end traceability.
Key & Certificate Events
Section titled “Key & Certificate Events”Tracked lifecycle events include:
- Key generation
- Key rotation
- Key revocation
- Key activation/deactivation
Certificates
Section titled “Certificates”- Certificate upload
- Certificate activation
- Certificate expiration
- Certificate revocation
This ensures cryptographic lifecycle accountability.
Filtering & Search
Section titled “Filtering & Search”The interface supports:
- Date range filtering
- Actor filtering
- Status filtering
- Action type filtering
- Keyword search
This allows rapid incident investigation and compliance reporting.
Export Capabilities
Section titled “Export Capabilities”Audit events can be exported for:
- Compliance audits
- Forensic investigations
- SIEM ingestion
- Long-term archival
Supported export format:
- CSV
Compliance Alignment
Section titled “Compliance Alignment”Audit logging supports major frameworks:
- SOC 2
- ISO 27001
- PCI DSS
- NIST controls
The platform records:
- Who performed an action
- What was executed
- When it occurred
- Which resource was affected
- Whether it succeeded
Security Properties
Section titled “Security Properties”Audit events are designed with:
- Tamper resistance
- Role-based access control
- Immutable event storage
- Complete lifecycle coverage
No critical platform action occurs without being recorded.
Why Audit Events Matter
Section titled “Why Audit Events Matter”Audit visibility provides:
- Regulatory compliance evidence
- Incident response capability
- Insider threat detection
- Governance enforcement validation
- Full operational transparency
In enterprise code signing, audit integrity is not optional — it is foundational.