Microsoft AD CS
Microsoft AD CS Integration
Section titled “Microsoft AD CS Integration”Integrate Microsoft Active Directory Certificate Services (AD CS) with SSL-CLM to:
- Discover existing certificates
- Sync certificate templates
- Issue certificates
- Revoke certificates
- Maintain continuous CA refresh
SSL-CLM integrates with Microsoft AD CS using a Windows Agent that executes native certificate enrollment operations locally and relays results securely to the platform.
Architecture
Section titled “Architecture”The SSL-CLM Agent must run on a domain-joined Windows server.
SSL-CLM Platform││ (mTLS, Pull-Based Jobs)▼Windows SSL-CLM Agent││ (WinRm Command Line)▼Microsoft AD CSStep 1 — Verify AD CS Installation
Section titled “Step 1 — Verify AD CS Installation”Confirm AD CS role is installed and running.
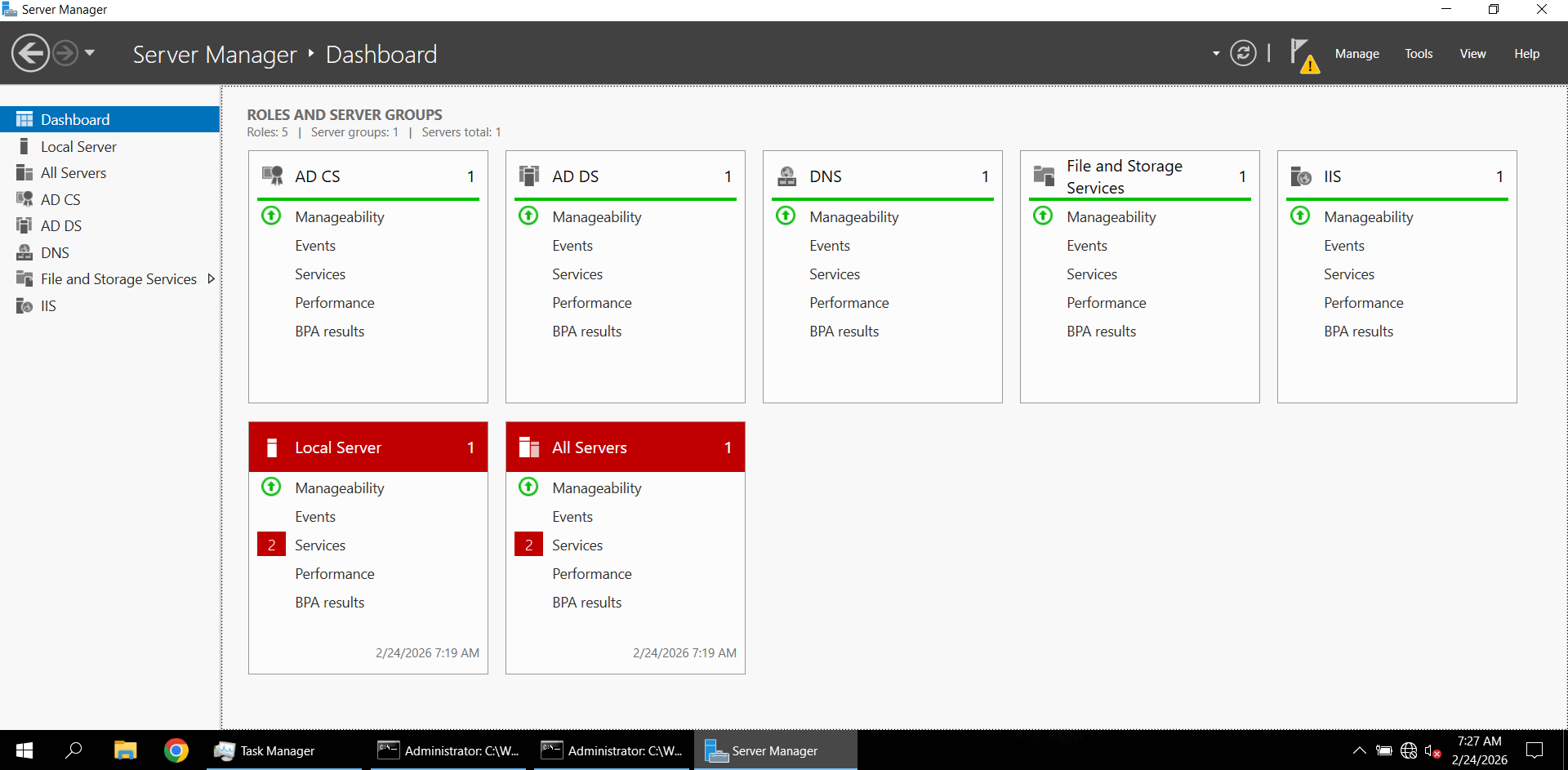
Open the Certification Authority console:
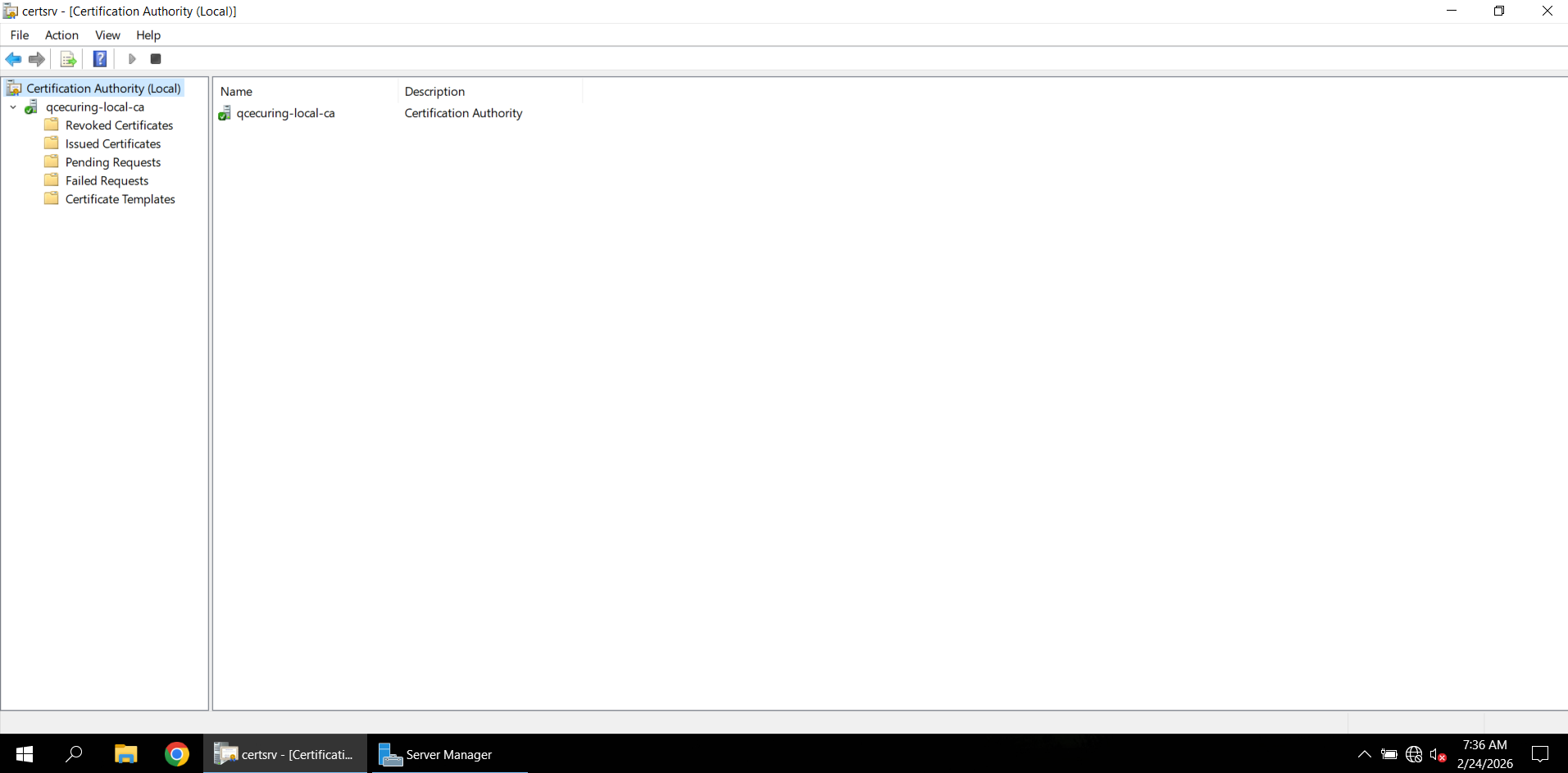
You should see your CA (e.g., qcecuring-local-ca).
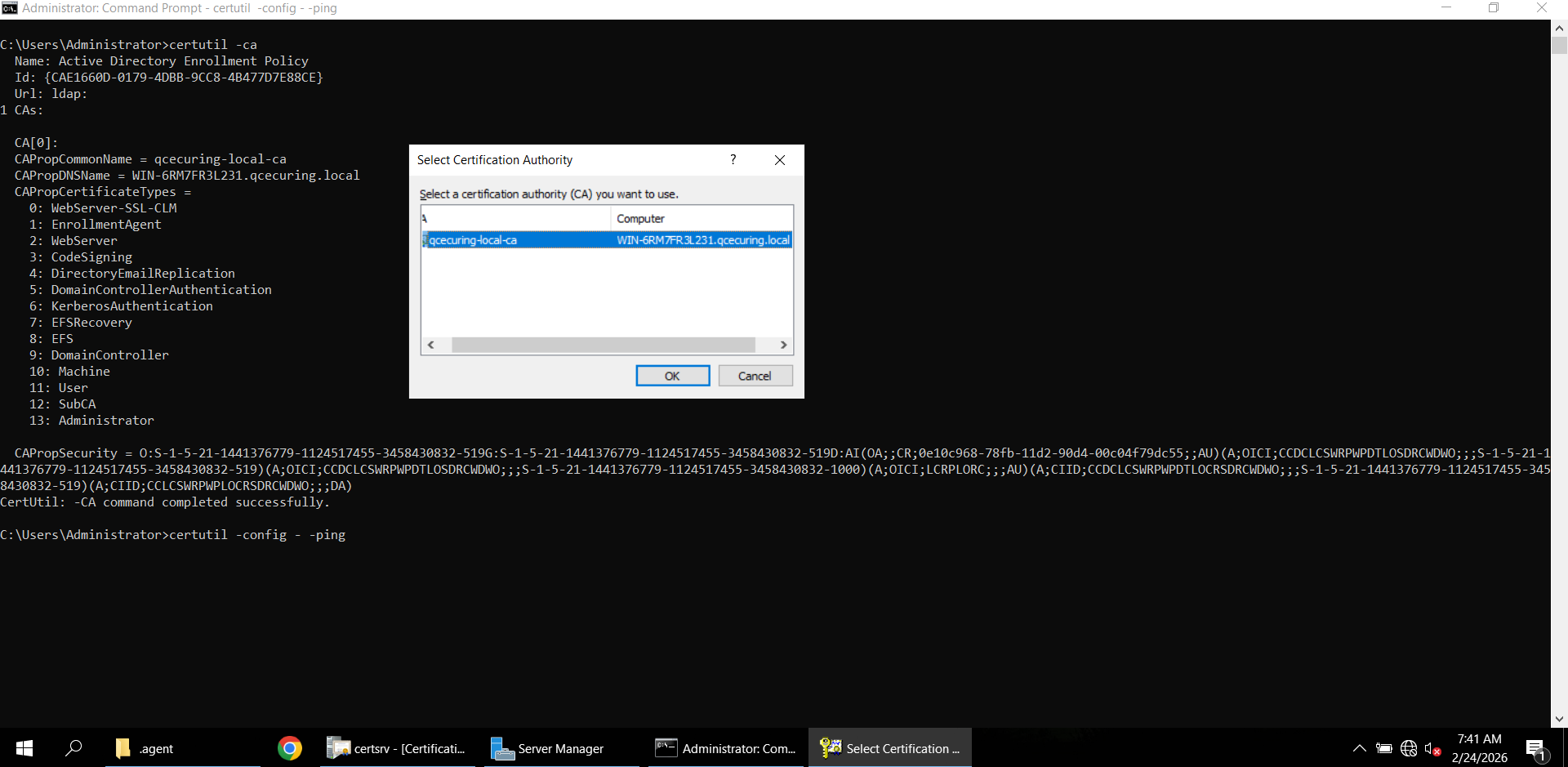
Step 2 — Verify CA Connectivity
Section titled “Step 2 — Verify CA Connectivity”From the Windows Agent server:
certutil -ping -config "WIN-6RM7FR3L231\qcecuring-local-ca"Successful output:
If you receive RPC Server Unavailable:
- Check TCP 135
- Verify firewall
- Ensure CA service is running
- Confirm DCOM permissions
Step 3 — Create Connector Config
Section titled “Step 3 — Create Connector Config”Navigate:
Configuration → Connector Configs → New ConnectorConfigure:
- Vendor: MSCA Agent
- Type: Agent Gateway
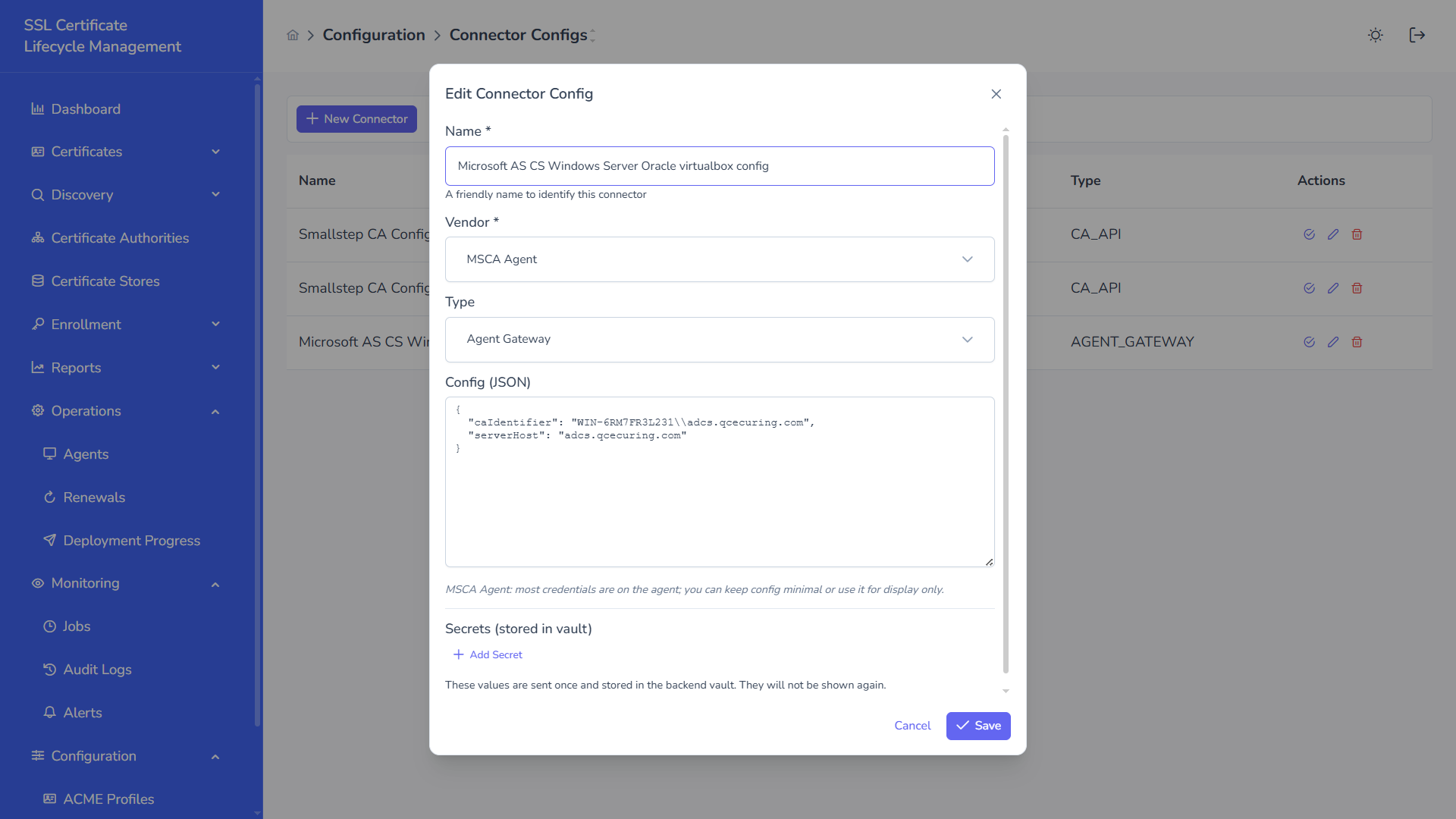
Example JSON:
{ "caIdentifier": "WIN-6RM7FR3L231\\qcecuring-local-ca", "serverHost": "WIN-6RM7FR3L231"}Step 4 — Create Certificate Authority Instance
Section titled “Step 4 — Create Certificate Authority Instance”Navigate:
Discovery → Certificate Authorities → New Certificate AuthoritySelect:
- Type: Microsoft CA
- Connector: MSCA Agent Gateway
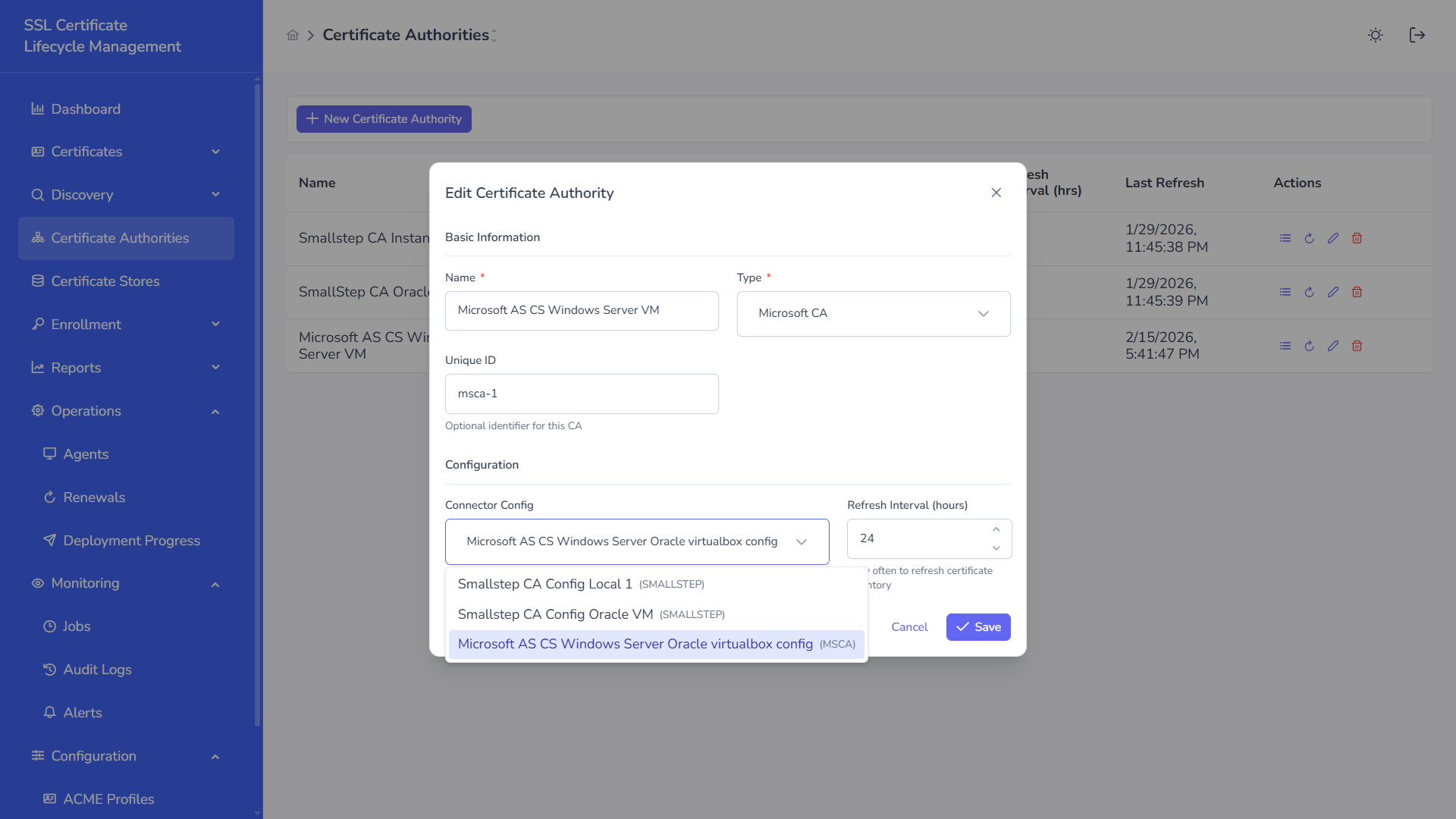
Save the configuration.
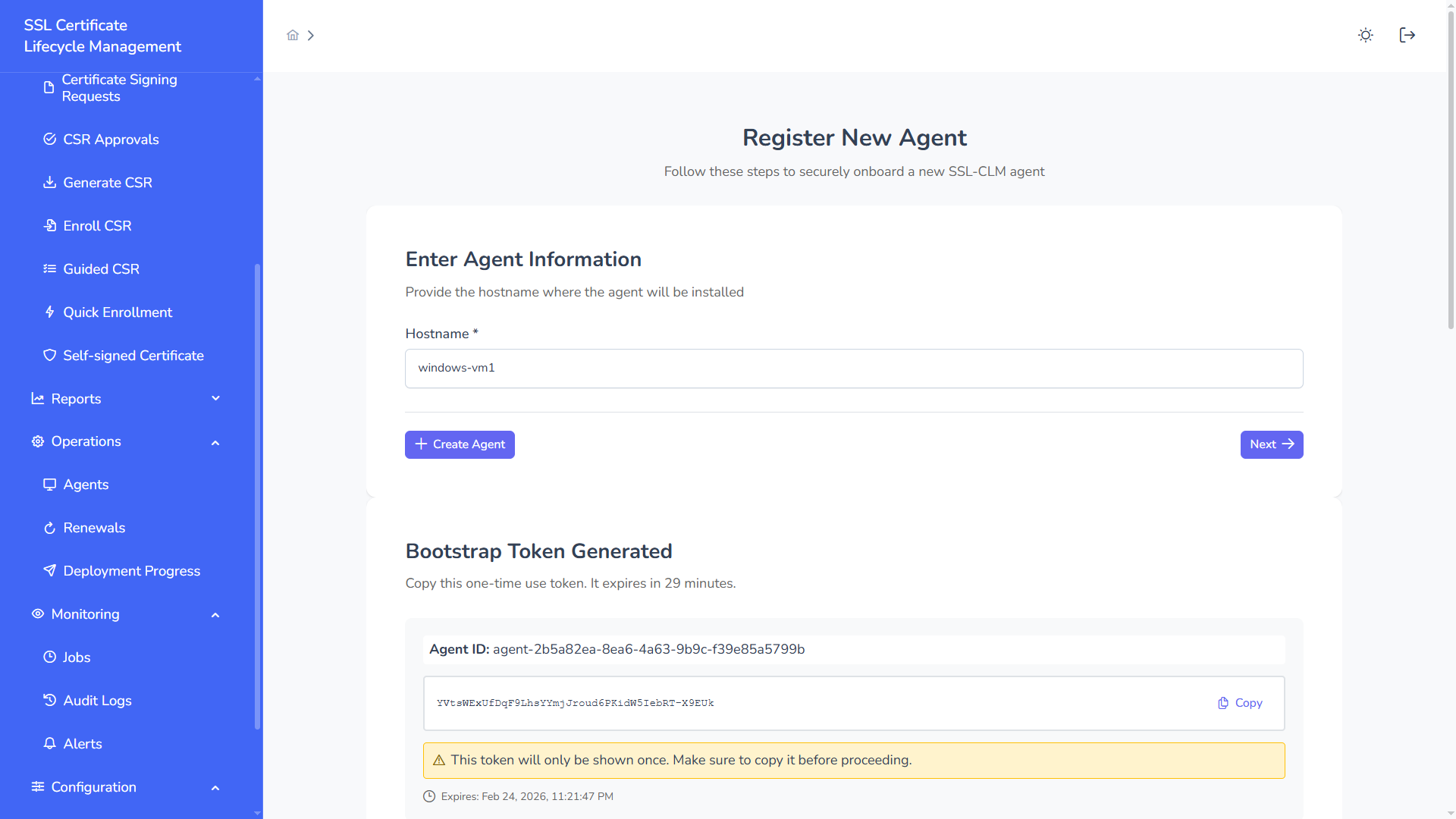
Step 5 — Register SSL-CLM Agent
Section titled “Step 5 — Register SSL-CLM Agent”Navigate:
Operations → Agents → Register New AgentGenerate bootstrap token.
Step 6 — Start the Windows Agent
Section titled “Step 6 — Start the Windows Agent”On the Windows server:
set API_URL=https://102.124.1.11:8080set AGENT_BOOTSTRAP_TOKEN=YVtsWExUfDqF9LhsYYmjJroud6PKidW5IebRT-X9EUK
set AGENT_MSCA_ENABLED=trueset AGENT_MSCA_CA_IDENTIFIER=WIN-6RM7FR3L231\qcecuring-local-caset ADCS_SERVER=WIN-6RM7FR3L231set ADCS_USERNAME=DomainUserset ADCS_PASSWORD=StrongPassword
java -jar ssl-clm-agent.jarAgent startup:
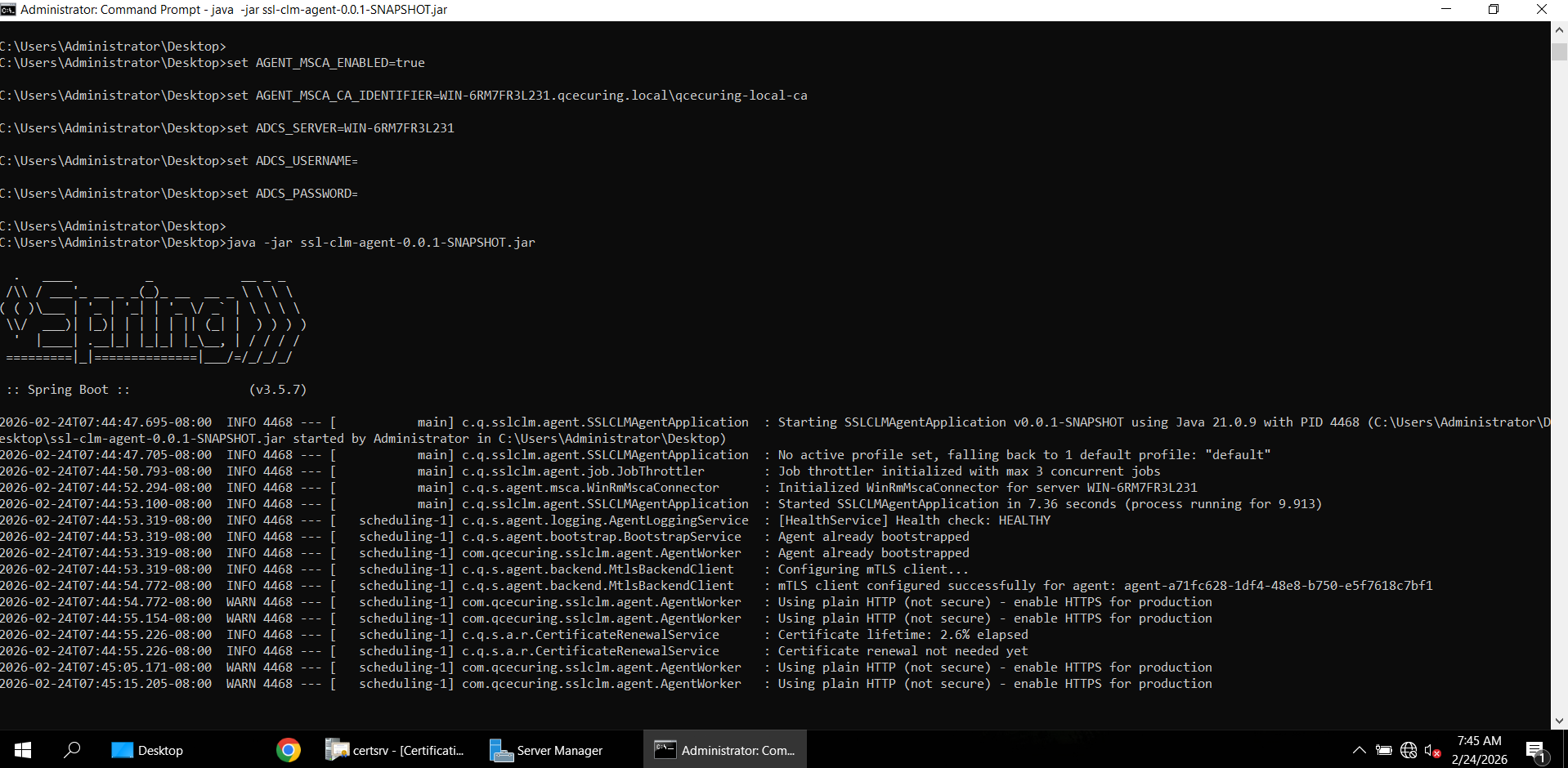
Agent should appear as ACTIVE in dashboard.
Step 7 — Load Templates
Section titled “Step 7 — Load Templates”In the CA instance, click Load Templates.
This triggers a CA_REFRESH job.
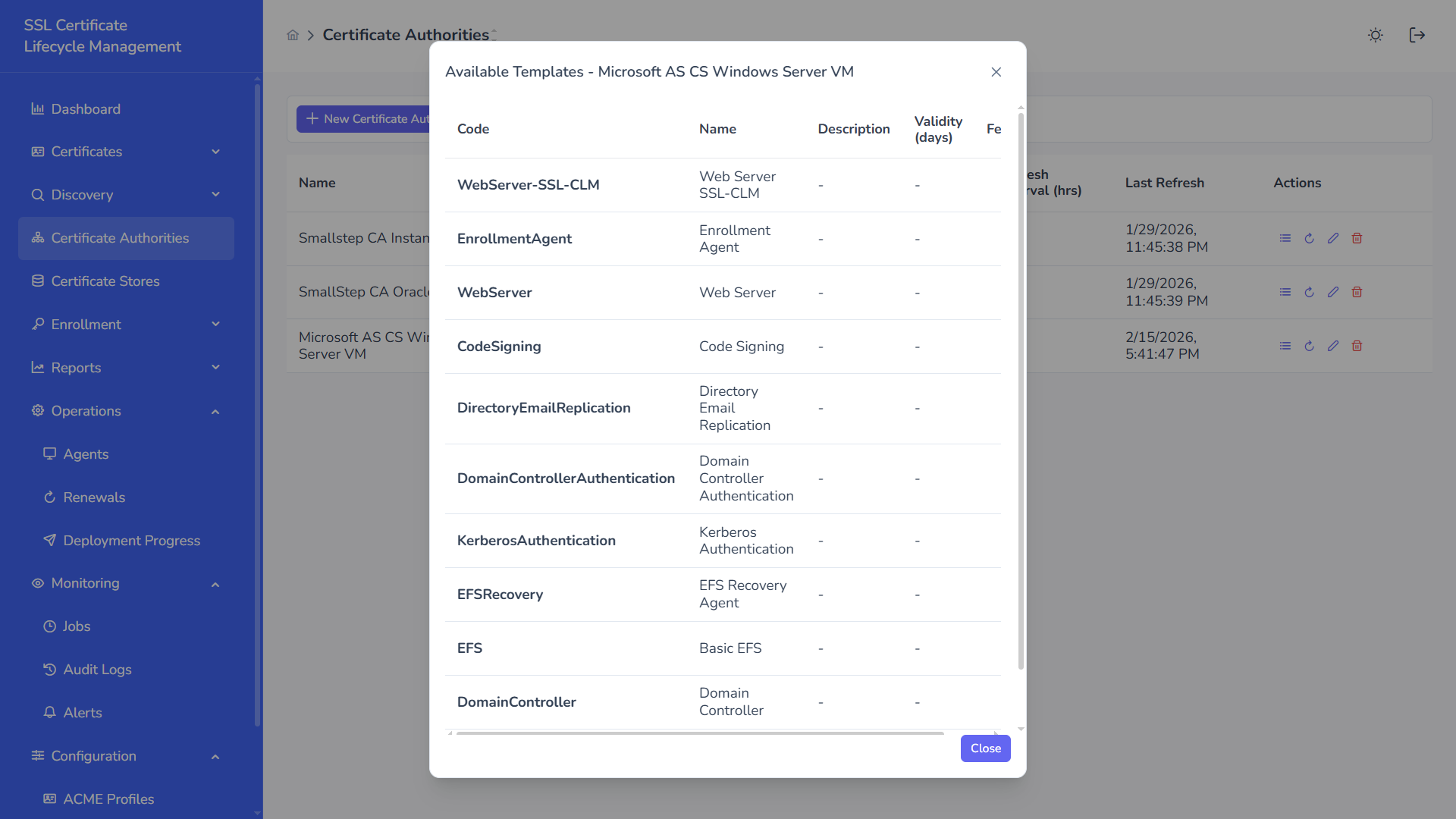
Templates such as:
- WebServer
- WebServer-SSL-CLM
- EnrollmentAgent
- CodeSigning
Will appear.
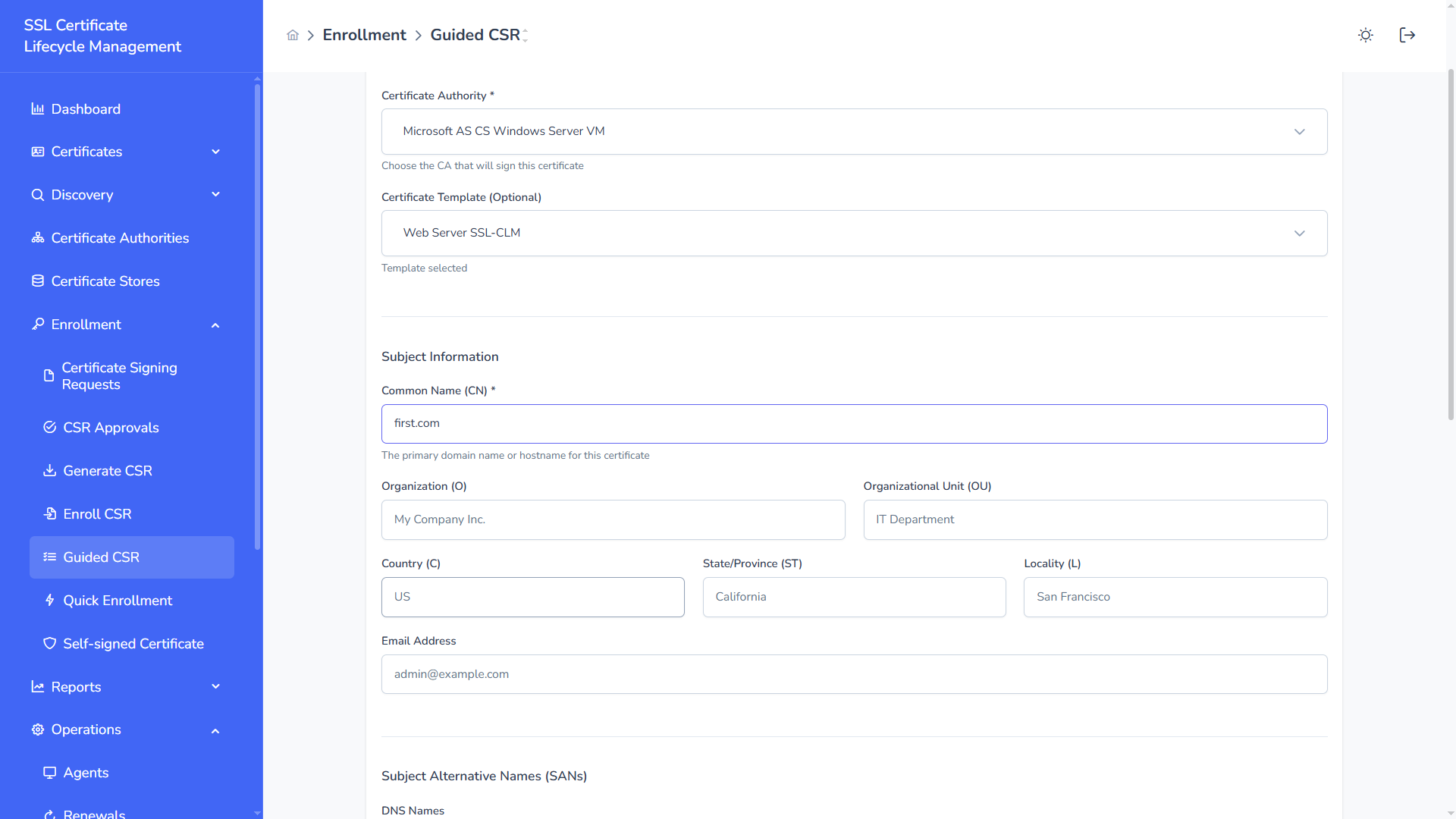
Step 8 — Submit CSR
Section titled “Step 8 — Submit CSR”Navigate:
Enrollment → Guided CSRFill certificate details and submit.
Step 9 — View Issued Certificate
Section titled “Step 9 — View Issued Certificate”After issuance, certificate status becomes Issued.
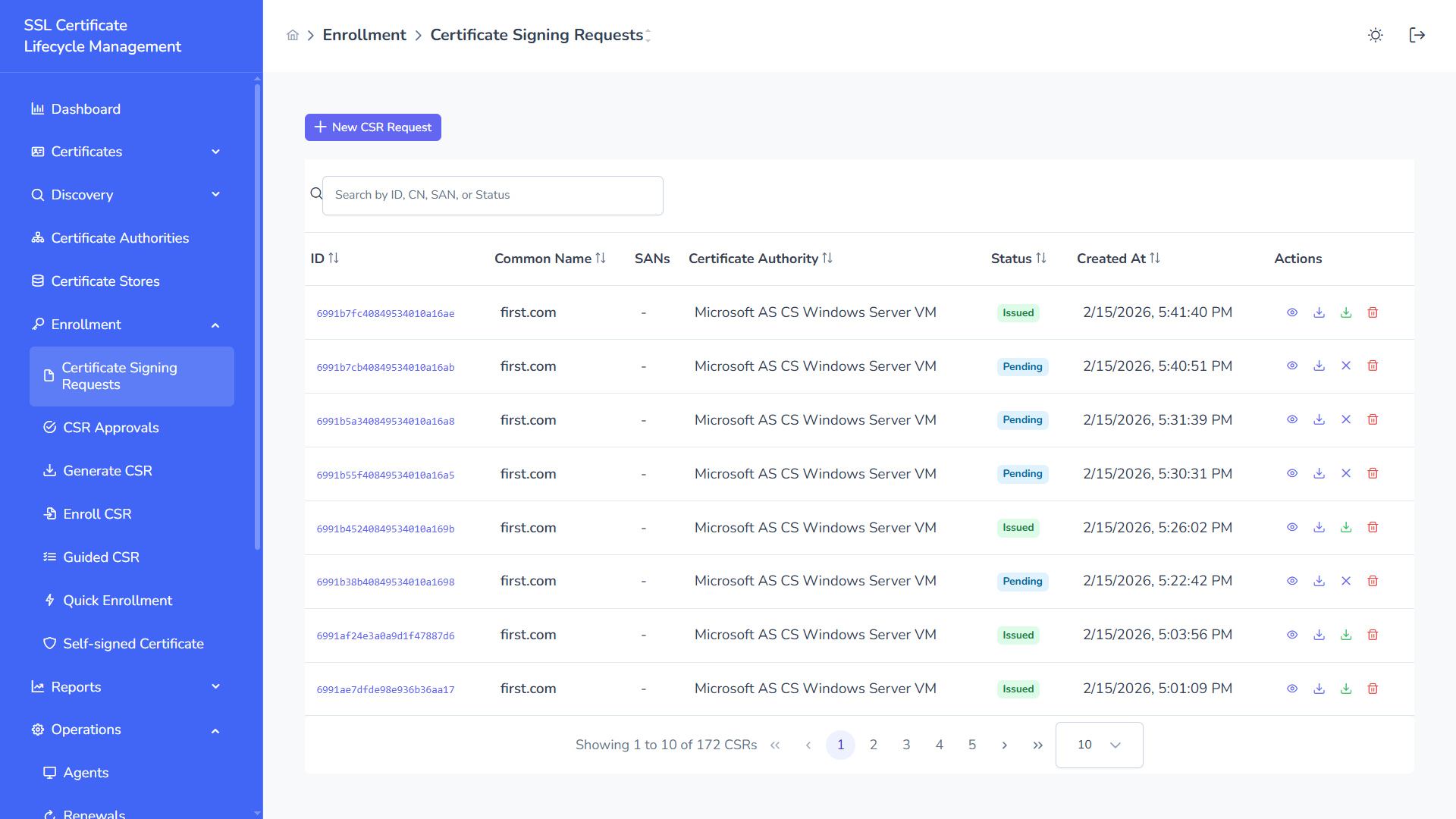
Flow:
- CSR stored in platform
ISSUE_CERTjob created- Agent enrolls via MSCA
- Certificate returned
- Inventory updated