Configuration
Configuration
Section titled “Configuration”The Configuration module centralizes global platform settings including ACME profiles, connectors, email notifications, and enforcement policies.
ACME Profiles
Section titled “ACME Profiles”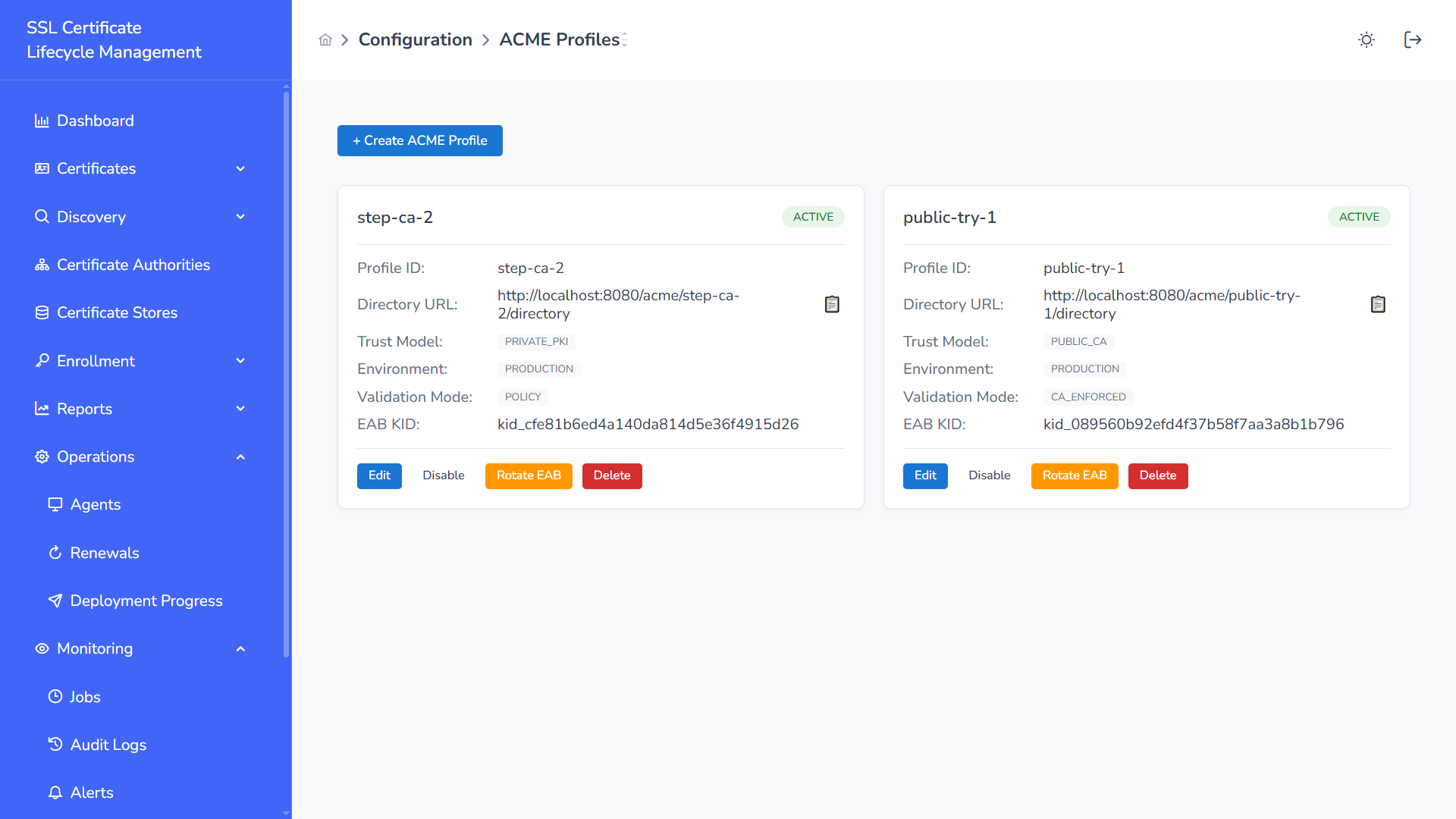
ACME Profiles define how the platform integrates with ACME-compatible certificate authorities.
Profile Attributes
Section titled “Profile Attributes”- Profile ID
- Directory URL
- Trust Model (PRIVATE_PKI / PUBLIC_CA)
- Environment (Production / Staging)
- Validation Mode
- EAB KID (External Account Binding)
Actions
Section titled “Actions”- Create ACME Profile
- Edit Profile
- Disable Profile
- Rotate EAB Credentials
- Delete Profile
ACME profiles are used during automated enrollment and renewal workflows.
Email Settings
Section titled “Email Settings”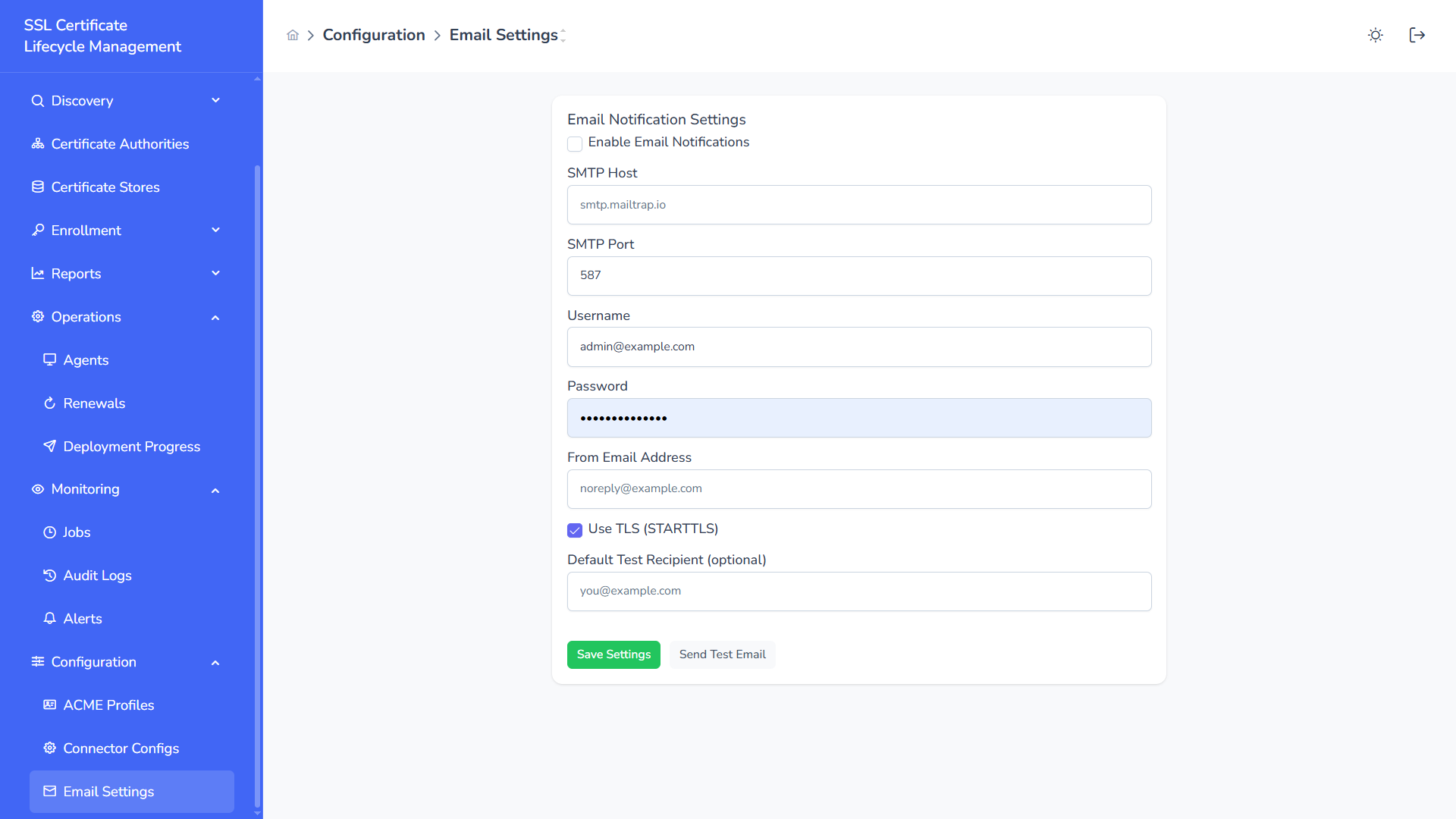
Email notifications provide proactive operational alerts.
SMTP Configuration
Section titled “SMTP Configuration”- Enable / Disable Email Notifications
- SMTP Host
- SMTP Port
- Username
- Password
- From Address
- TLS (STARTTLS)
- Default Test Recipient
Actions
Section titled “Actions”- Save Settings
- Send Test Email
Notification Triggers
Section titled “Notification Triggers”- Certificate Expiring
- Enrollment Failure
- Deployment Failure
- Agent Offline
- Renewal Errors
Email configuration ensures operational visibility beyond the platform UI.
Connector Configuration
Section titled “Connector Configuration”Configure integration with:
- Certificate Authorities (Microsoft CA, Smallstep, etc.)
- Agent Gateways
- Certificate Stores
Configurable Parameters
Section titled “Configurable Parameters”- API endpoints
- Authentication credentials
- JSON configuration payload
- Secret storage (vault-backed)
- Refresh intervals
- Retry policies
Connectors enable secure communication between SSL CLM and external systems.
Policy Enforcement
Section titled “Policy Enforcement”Define organizational certificate governance rules.
Enforced Controls
Section titled “Enforced Controls”- Minimum key size
- Allowed key algorithms
- Maximum validity period
- Required SAN entries
- Restricted domains
- Environment-based restrictions
Policies are validated during:
- CSR submission
- Certificate issuance
- Renewal workflows
- Deployment operations
Operational Considerations
Section titled “Operational Considerations”- Use Production vs Staging profiles appropriately
- Rotate EAB and credentials periodically
- Test SMTP configuration after changes
- Apply strict policies in regulated environments
The Configuration module governs trust, automation, and enforcement across the entire SSL certificate lifecycle.