Smallstep Step-CA
Smallstep Step-CA Integration
Section titled “Smallstep Step-CA Integration”Integrate Smallstep Step-CA with SSL-CLM to:
- Issue certificates
- Revoke certificates
- Sync certificate inventory
- Use secure JWK-based authentication
- Enable internal private PKI automation
Step-CA integrates directly using its REST API.
No Windows Agent is required.
Architecture Overview
Section titled “Architecture Overview”SSL-CLM Platform││ (HTTPS + JWK signed tokens)▼Smallstep Step-CA│▼Internal Certificate AuthoritySSL-CLM authenticates using a JWK Provisioner Private Key.
Step 1 — Install Step CLI
Section titled “Step 1 — Install Step CLI”Install Smallstep CLI on your CA server:
https://smallstep.com/docs/step-cli/installation
Verify:
step versionStep 2 — Initialize Step-CA
Section titled “Step 2 — Initialize Step-CA”Create a password file:
step-ca-password.txtExample:
123Initialize CA:
step ca init ^ --name "QCecuring Internal CA" ^ --dns step-ca-local.qcecuring.com ^ --address :9000 ^ --provisioner clm@qcecuring.com ^ --password-file step-ca-password.txtThis creates:
- Root certificate
- Intermediate certificate
- Default provisioner
- CA configuration
- PKI directory
Start Step-CA:
step-ca $(step path)/config/ca.jsonDefault API:
https://step-ca-local.qcecuring.com:9000Step 3 — Create Provisioners
Section titled “Step 3 — Create Provisioners”We separate provisioners for security.
Provisioner 1 — Admin (CLI usage)
Section titled “Provisioner 1 — Admin (CLI usage)”Used for manual certificate issuance.
Remove default:
step ca provisioner remove admin@qcecuring.comRecreate as JWK:
step ca provisioner add admin@qcecuring.com --type JWK --createTest:
step ca certificate google.com google.pem google.key \ --provisioner admin@qcecuring.comProvisioner 2 — CLM (Platform Integration)
Section titled “Provisioner 2 — CLM (Platform Integration)”Used by SSL-CLM.
Remove existing:
step ca provisioner remove clm@qcecuring.comCreate JWK keypair:
step crypto jwk create clm-pub.json clm-priv.json \ --kty EC \ --crv P-256 \ --no-password \ --insecureAdd provisioner:
step ca provisioner add clm@qcecuring.com ^ --type JWK ^ --public-key clm-pub.jsonVerify:
step ca provisioner listStep 4 — Extract Private Key for SSL-CLM
Section titled “Step 4 — Extract Private Key for SSL-CLM”The platform requires the JWK private key.
type clm-priv.jsonThis JSON will be used inside SSL-CLM connector configuration.
⚠️ Store securely.
Step 5 — Create Connector Config in SSL-CLM
Section titled “Step 5 — Create Connector Config in SSL-CLM”Navigate:
Configuration → Connector Configs → New ConnectorSelect:
- Vendor: Smallstep (Local CA)
- Type: API CA
Configuration JSON:
{ "provisionerName": "clm@qcecuring.com", "baseUrl": "https://step-ca-local.qcecuring.com:9000", "provisionerKeyId": "<kid-from-jwk>", "provisionerJwk": { "kty": "EC", "crv": "P-256", "kid": "<kid>", "x": "<x>", "y": "<y>", "d": "<d>" }}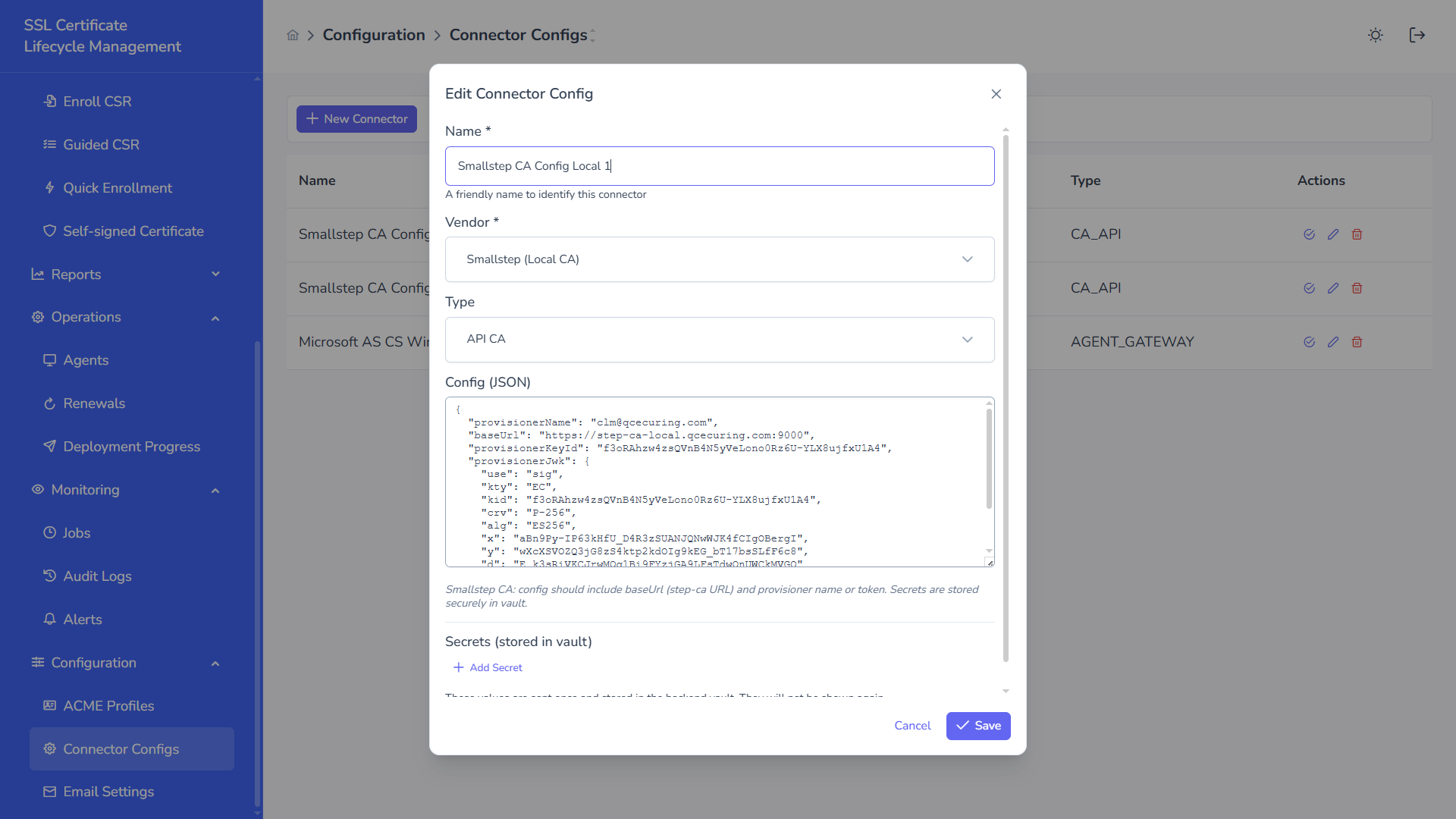
Secrets are stored securely in backend vault.
Save connector.
Step 6 — Create Certificate Authority Instance
Section titled “Step 6 — Create Certificate Authority Instance”Navigate:
Discovery → Certificate Authorities → New Certificate AuthoritySelect:
- Type: Smallstep CA
- Connector Config: Smallstep CA Config Local 1
- Refresh Interval: 24 hours
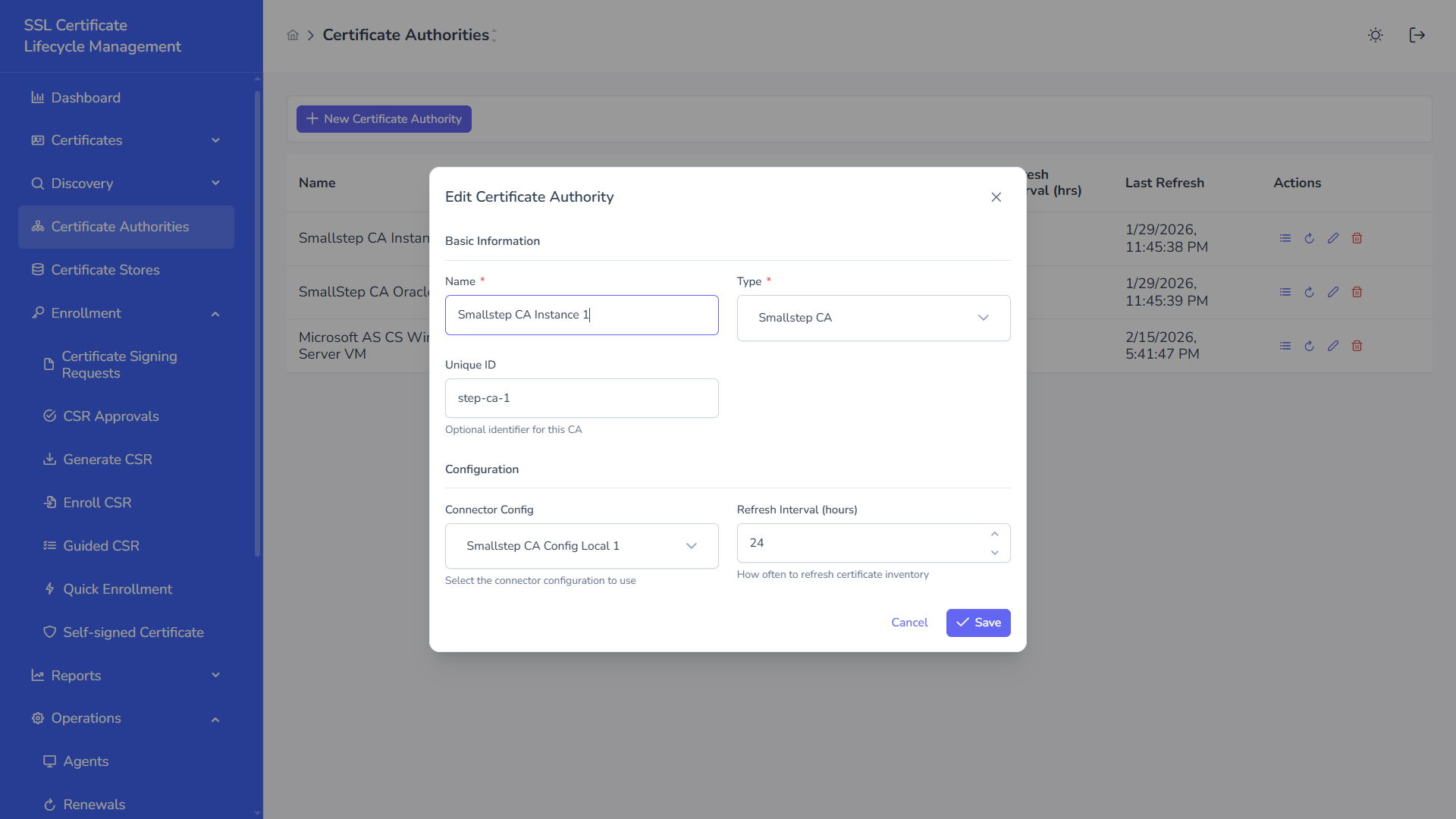
Save.
Step 7 — Load Templates
Section titled “Step 7 — Load Templates”Click:
Load TemplatesSSL-CLM will:
- Call Step-CA API
- Retrieve provisioners
- Sync certificate capabilities
Step 8 — Issue Certificate
Section titled “Step 8 — Issue Certificate”Navigate:
Enrollment → Guided CSRSelect:
- Certificate Authority
- Subject details
- SAN entries
Submit.
Flow:
- CSR stored in SSL-CLM
- API call made to Step-CA
- JWK token signed
- Certificate issued
- Stored in platform
Status becomes:
IssuedStep 9 — Revoke Certificate
Section titled “Step 9 — Revoke Certificate”When revocation requested:
- Platform calls Step-CA revoke API
- Status updated in SSL-CLM
- Next refresh sync confirms revocation
Security Model
Section titled “Security Model”Authentication
Section titled “Authentication”- JWK signed tokens
- No password-based auth
- Key-based API access
Recommended
Section titled “Recommended”- Enable HTTPS with trusted certificate
- Restrict CA port exposure
- Store JWK private key in vault
- Rotate provisioner keys periodically
Troubleshooting
Section titled “Troubleshooting”Error: Unauthorized
Section titled “Error: Unauthorized”- Check provisioner name
- Verify
kidmatches public key - Confirm private key is correct
Error: Connection Refused
Section titled “Error: Connection Refused”- Confirm Step-CA running
- Verify port 9000 open
- Check DNS resolution
Provisioner Not Found
Section titled “Provisioner Not Found”Run:
step ca provisioner listEnsure clm@qcecuring.com exists.
Operational Best Practices
Section titled “Operational Best Practices”- Separate admin and automation provisioners
- Use EC P-256 keys
- Restrict JWK usage scope
- Enable scheduled inventory refresh
- Backup PKI directory