SSL-CLM Agent
SSL-CLM Operational Agent
Section titled “SSL-CLM Operational Agent”The QCecuring SSL-CLM Agent enables secure, distributed certificate lifecycle execution across your infrastructure.
It runs locally on servers to:
- Integrate with on-prem Certificate Authorities (e.g., MSCA)
- Execute certificate issuance and revocation
- Refresh CA inventory and templates
- Submit PKI snapshots to the SSL-CLM platform
- Maintain periodic heartbeat with the backend
- Execute lifecycle jobs in a pull-based model
The agent does not expose inbound ports and does not store CA private keys.
All operations are executed securely via outbound communication.
Supported Platforms
Section titled “Supported Platforms”- Windows Server 2016+
- Linux (Ubuntu, RHEL, Debian, SUSE)
Prerequisites
Section titled “Prerequisites”- Java 21 or later
- Network access to SSL-CLM backend
- Bootstrap token (for first registration)
Optional (Production):
- mTLS client certificate
- HTTPS-enabled backend
- On-prem CA access (e.g., Microsoft ADCS)
Installation
Section titled “Installation”Download the agent from:
Agent Management → Download AgentOr obtain the JAR file:
ssl-clm-agent-0.0.1-SNAPSHOT.jarRunning the Agent
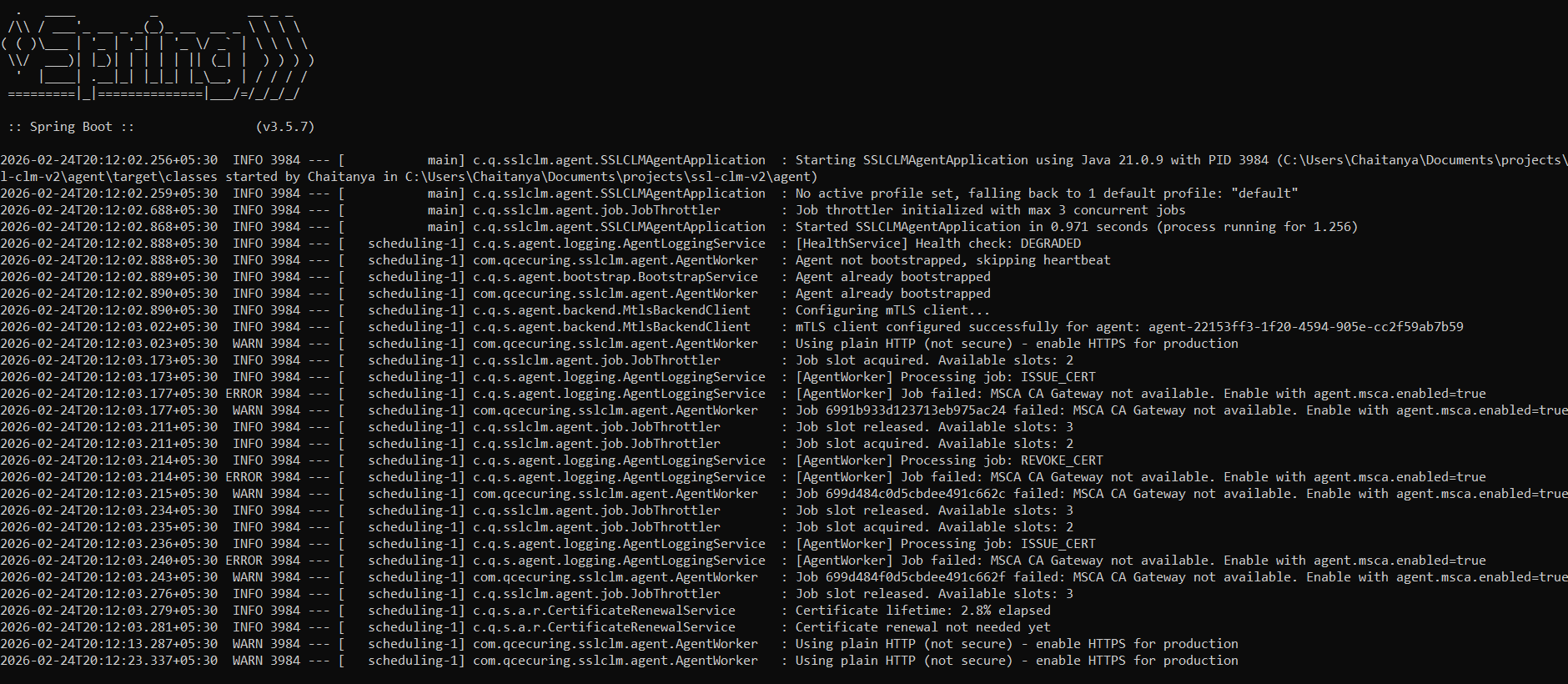
Section titled “Running the Agent”java -jar ssl-clm-agent.jarWhen started successfully, the agent:
- Registers using bootstrap token
- Receives a unique
agentId - Begins periodic heartbeat
- Starts polling for lifecycle jobs
- Executes assigned certificate operations
First-Time Registration (Bootstrap)
Section titled “First-Time Registration (Bootstrap)”The agent requires a bootstrap token for initial registration.
Example:
java -jar ssl-clm-agent.jar \ --backend.url=http://localhost:8080 \ --bootstrap.token=YOUR_BOOTSTRAP_TOKENRegistration flow:
- Agent sends bootstrap token to backend
- Backend validates token
- Backend issues agent identity + access token
- Agent stores credentials locally
- Future communication uses mTLS or issued token
Configuration
Section titled “Configuration”The agent can be configured via:
agent.properties- Environment variables
- Command-line arguments
Example Configuration (agent.properties)
Section titled “Example Configuration (agent.properties)”backend.url=http://localhost:8080
# Job executionagent.jobs.fixedDelayMs=10000agent.heartbeat.fixedDelayMs=30000
# Bootstrapbootstrap.token=CHANGE_ME
# MSCA Integration (optional)agent.msca.enabled=trueagent.msca.ca-identifier=corp-ca
# Optional mTLS (recommended in production)backend.mtls.enabled=falsebackend.mtls.client-cert-path=backend.mtls.client-cert-password=backend.mtls.ca-cert-path=
logging.level=INFOEnvironment Variables
Section titled “Environment Variables”export BACKEND_URL=http://localhost:8080export BOOTSTRAP_TOKEN=your_bootstrap_tokenIn production environments, use secure secret management for tokens and certificates.
Job Execution Model (Pull-Based)
Section titled “Job Execution Model (Pull-Based)”The agent uses a secure pull model:
- Poll backend for jobs
- Execute job locally
- Submit result
- Update job status
No inbound firewall rules required.
Supported Job Types
Section titled “Supported Job Types”CA_REFRESH
Section titled “CA_REFRESH”- Fetch certificates from on-prem CA
- Retrieve templates
- Submit PKI snapshot to backend
ISSUE_CERT
Section titled “ISSUE_CERT”- Receive CSR
- Submit to CA
- Retrieve issued certificate
- Return result to backend
REVOKE_CERT
Section titled “REVOKE_CERT”- Receive serial number
- Execute revocation on CA
- Return revocation result
Safe Mode
Section titled “Safe Mode”If:
- mTLS certificate is revoked
- Agent identity is invalid
- Backend returns authorization failure
The agent:
- Stops executing jobs
- Stops heartbeat
- Enters fail-closed state
- Requires re-bootstrap
Running as a Service
Section titled “Running as a Service”Windows
Section titled “Windows”Install as a Windows service using NSSM or similar.
Start-Service QCecuring-SSL-CLM-AgentStop-Service QCecuring-SSL-CLM-AgentGet-Service QCecuring-SSL-CLM-AgentLinux (systemd)
Section titled “Linux (systemd)”sudo systemctl start ssl-clm-agentsudo systemctl status ssl-clm-agentsudo systemctl enable ssl-clm-agentCommunication Model
Section titled “Communication Model”The agent communicates with backend via:
- HTTPS (default)
- Optional mTLS (recommended in production)
- JWT-based authentication after bootstrap
Default intervals:
- Heartbeat: 30 seconds
- Job polling: 10 seconds
- Health check: 5 minutes
Verification
Section titled “Verification”To verify the agent is running:
- Ensure process is active
- Confirm Registered Agents page shows status
ACTIVE - Trigger a CA_REFRESH job and confirm execution
- Monitor job logs in dashboard
Security Best Practices
Section titled “Security Best Practices”- Enable HTTPS
- Enable mTLS in production
- Rotate bootstrap tokens
- Restrict outbound network access
- Deploy one agent per on-prem CA
- Monitor job execution logs
Next Steps
Section titled “Next Steps”- Configure CA integration
- Create certificate templates
- Test issuance workflow
- Test revocation workflow
- Enable scheduled CA refresh jobs